Every element of civilization has been impacted by technological breakthroughs. Everybody generates a lot of data when using networks every day. Perhaps some questions pop up in front of your eyes. You might be interested in learning how to access mobile phone data from a distance. Or is there a method to use WiFi to spy on a phone?
Without a doubt, the answer is yes. In this article, you can learn how to access Android or iOS devices through Wi-Fi. Let's go for it

Part 1. How to Break into Someone's iPhone by WiFi
There are various ways you can access someone's iPhone through WiFi. One of those ways is by using some monitoring tools. One of such tools is FoneWatcher, considered the best among equals.
With FoneWatcher iPhone Monitoring, you can enjoy many benefits as a user. However, suppose you are just hearing about FoneWatcher for the first time. In that case, you should consider yourself lucky because this app will provide you with whatever you need when it comes to monitoring someone else.

- Hidden and undetactable. No jailbreak reuqired
- Read all text messages/iMessages without knowing. The deleted ones can also be seen
- Track iPhone location in both map and list view, clearly know the lcoation
- Check call history even deleted and Safari browsing history and bookmarks on iPhone.
- Photos, videos, notes, voice memos, reminders and calendar can be chedked.
3-Step Guide to Access iPhone through WiFi with FoneWatcher
Before you can enjoy the benefits of FoneWatcher, there are some basic steps you first have to take. Mind you, FoneWatcher is a premium tool, so you might have to purchase some plans that suit your needs. Consider the following steps:
Step 1. Register a FoneWatcher Account
You need to create an account with FoneWatcher before you can enjoy its incredible features. From here, you will provide the necessary details before moving on to the next stage.
Step 2. Download the App
After registration, the next step is to download the application to the device. Follow the guidance to finish the installation. Sync the iPhone data with USB at first time, and then you can check iPhone data under the same Wi-Fi.
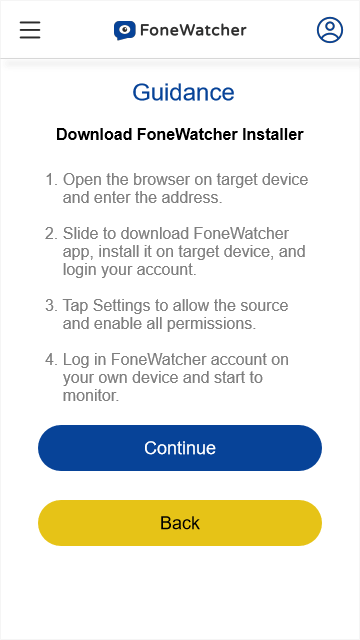
Step 3. Monitor Target iPhone on FoneWatcher Dashboard
This is the final step. Now you can easily monitor the person's iPhone from the dashboard of your FoneWatcher account. You can easily see all the activities on the phone, including the person's browser history.
Part 2. How to Spy on Android Phone through WiFi
Man-in-the-middle attacks are pretty common in the cybersecurity attack space. The MITM allows attackers to eavesdrop on what two targets are communicating about. The attack exists between two legitimately communicating hosts, allowing the attacker to listen to a conversation they were not supposed to listen to – that is where the title man-in-the-middle comes from.
Types of MITM Attacks
There are various ways a hacker can use the man-in-the-middle system to attack a target. The following is a list of the common types of MITM attacks:
- APR Spoofing
- mDNS Spoofing
- DNS Spoofing
Also, below are some MITM attack techniques:
- Sniffing
- Packet Injection
- Session Hijacking
- SSL Stripping
How to Spy on Android Phone with MITM Attack
Using MITM attacks to spy on Android phones has become relatively easy these days. The following are the steps:
- Step 1: Create an account
- Step 2: Install the software on the android devices of the two hosts
- Step 3: Begin to monitor the activities of the two hosts, i.e., you can read their conversation.
MITM attack allows you to act like the other person in the conversation. Basically, when A and B are having a conversation, you can be the middle person. That means A will think you are B, and B will believe you are A. With this, you can gain information from both parties simultaneously.
Part 3. A Better Way to Monitor Android Phone
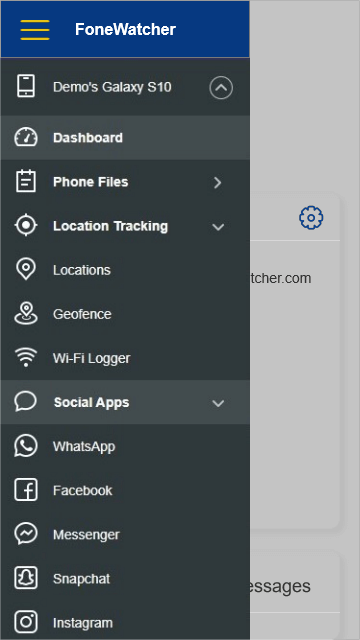
There are various reasons why FoneWatcher is the best tool for you if you intend to monitor someone else's activities. With all the fantastic benefits and features associated with FoneWatcher Android Monitoring, you will agree that it is the best monitoring software there is. Below are the reasons many people are choosing FoneWatcher:

- 100% hidden with steal mode, no root needed
FoneWatcher is 100% stealth. Your target will never suspect what is going on, except, of course, you decide to tell the person yourself. But besides that, whatever activity you are doing or viewing remotely will remain hidden from the target.
- Track and sync real-time location as well as provide history location
FoneWatcher will not only track the location of your target in real-time but also provide the locations of all where your target has been. All this will be done without the target ever knowing it is happening.
- See messages sent, received and deleted
Another incredible perk with using FoneWatcher is that you will have access to all the messages your target has received and sent; even the ones deleted will be available for you to see. This means that your target will not be able to hide anything from you.
- Monitor 10+ social media apps
With FoneWatcher, you can also monitor your target's social media accounts on WhatsApp, Facebook, Messenger, Instagram, Snapchat, Discord, etc. Whatever message, photos, or videos the person sent or received will be available to you. Even if the target deletes them, you will still have access to the information.
- Capture screenshots and use phone camera remotely
This feature is available to only a few monitoring tools. With FoneWatcher, you can make screenshots of the activities going on in your target's device. In addition, you can remotely activate the camera of your target's phone to take pictures remotely.
- Record details on phone
FoneWatcher is regarded as the best phone monitoring app bescause users will miss no details. You can use it to record phone calls, record phone screens, ans record phone surroundings.
- Get instant notifications.
FoneWatcher allows you to set up geofence. When the person is in or out of the zone, the alerts will be sent to you. You can also put in the keywords you care about and get notified.
Tips: How to Prevent Phone Hacking through WiFi
An average person believes that WiFi hacking is just a process of a hacker breaking into their WiFi network. But WiFi hacking is more than that; a professional hacker can use WiFi to track users by their device, use phishing attacks to compromise passwords, and expose information about where a person travels or works. You can reduce your risk of getting attacked by following the steps below:
- Remove useless network from your preferred network list
- Keep your local traffic encrypted by using a VPN
- Deactivate auto-connect when joining networks
- Never use hidden networks
- Disable WPS functionality on routers
- Never re-use passwords for WiFi
- Isolate clients to their own subnet
Conclusion
While the method of accessing another phone can be alien to an average person, it is very possible. And you can achieve your goals easily by subscribing to FoneWatcher for easier accessibility and the ability to enjoy other features. Try the FoneWatcher premium today. You will be glad you consider this tool, for it has everything you may require in monitoring software.
 Phone Monitor
Phone Monitor Phone Track
Phone Track Social Media
Social Media Remote Control
Remote Control Parental Control
Parental Control Revealing Cheating
Revealing Cheating Alternatives Reviews
Alternatives Reviews iOS News
iOS News